Passwordless Authentication
What does Passwordless mean?
Paul Ford makes a great case in Wired https://lnkd.in/ghpgi_sg for why the tech industry should stop absolutely everything else it is doing— self-driving cars, large language models, spyware, etc—and figure out how to put passwords behind us.
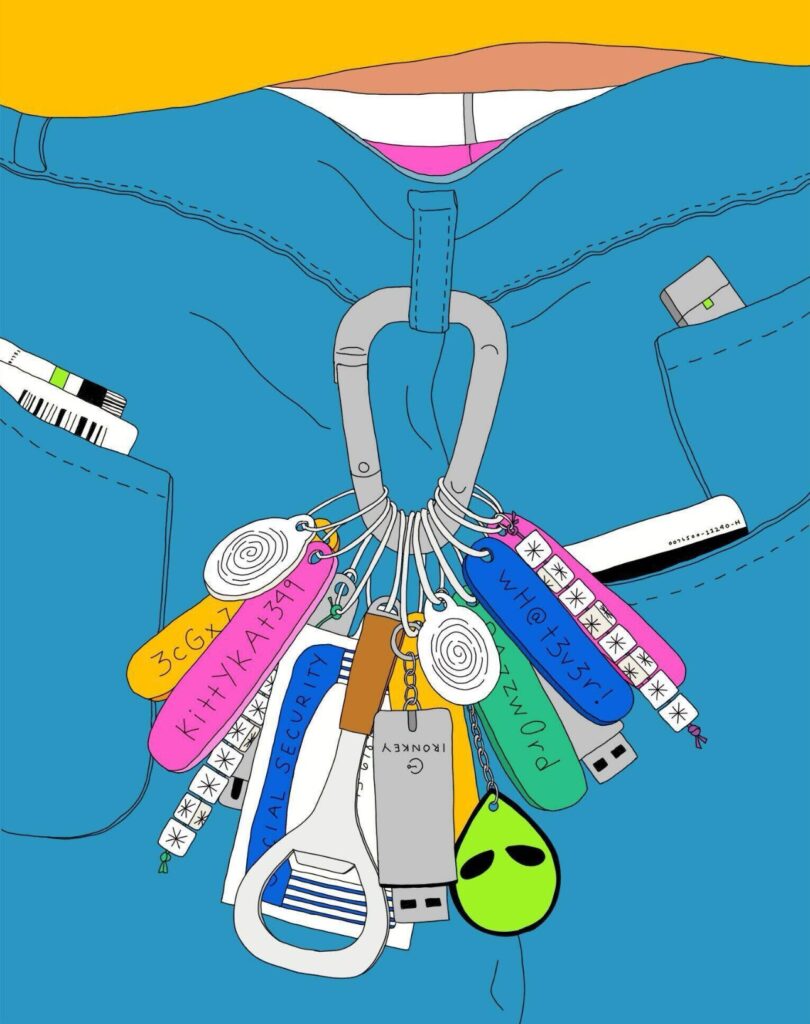
“It does feel that everything is so hackable, with ever-heavier layers of security. Verification codes SMSed and generated by USB keys, anything to keep the wolves at bay. If quantum computers ever happen, with their magic large-number-factoring abilities, they will blow up our entire secure, encrypted communications layer. It’s game over— all our protection just gets thrown into the garbage without an obvious fix. Here I am, surrounded by vulnerable devices that I don’t fully control but also can’t protect. My washing machine is probably secretly a web server, and one day someone will use it to mine crypto.”
The Financial Services industry is one of the biggest culprits, still relying on passwords for the most sacred of things, our money. Fortunately, with Moroku Money, our clients are at the right end of the ladder with our identity and security platforms including that of our brilliant partnership with FrankieOne
In an attempt to resolve the friction and make systems more secure, you may have heard about passwordless authentication. At Moroku we’ve been preparing to make it the default authentication mechanism across our systems and products.
While the technology and standards required to implement Password less auth have been available for quite a while (the WebAuthn standard was first published in 2016) you probably haven’t converted your own apps to Passwordless yet. We and a lot of other people now think it’s time to start looking at that.
As is often the case with new technologies adoption rates slowly build until a tipping point is reached. Early adoptors had to roll their own implementations and deal with legacy browser and device versions which did not support the WebAuthn standard. The steady stream of authentication products now offering passwordless as an option and the announcement by Google that they are rolling out it out across their platforms are indications adoption rates are increasing.
Why
So why should you start using Passwordless authentication in your apps? Put simply – because it provides a stronger , more secure authentication solution with a better user experience. Attack vectors such as phishing, password theft, and replay attacks are no longer a concern. You may be thinking – this sounds too good to be true – or why didn’t we do this earlier? It’s worth taking a step back and looking at how we arrived at the current status.
Back in the early days of the web – the HTTP standards included something called Basic Auth as a mechanism for identifying users. The term basic was very appropriate. Usernames and passwords were Base64 encoded (NOT encrypted). High value transactions did not exist on the web back then, and Basic Auth was never intended to be used in such cases. Standards such as OAuth were subsequently developed to provide a strong authentication solution. In fact the password frant flow was included in the original OAuth standards to provide a migration path for existing websites. The intent was that it would be used to transition to other authentication mechanisms that did not require passwords. This did not happen as quickly as the autheors had hoped.
Meanwhile, as the compute resources available to malicious actors increased exponentially attacks became more sophisticated. Password databases became honeypots for fraudulent transactions and identity theft. The risks for businesses responsible for protecting their customer’s funds and data increased accordingly.
To combat these attacks service providers enforced password restrictions (length and complexity were increased) and added multiple factor authentication (one time passwords, biometric prints). The modern internet user now has on average around 100 passwords. Third party apps were developed to manage these – LastPass, Google Authenticator, Authy to name a few). Which brings us to the present – and the current shift towards Passwordless authentication.
How
So how do Passwordless authentication solutions work?
The details vary slightly across implementations but at high level they replace usernames and passwords with public key based alternatives. Private keys are stored on a users device and protected with biometric auth. Service providers store the associated public key. There is no longer a centralised database of secrets, users do not have to remember a password, and a much stronger private key is used in the identity verification process. This is how Passwordless solutions provide stronger authentication with a better user experience.
If you are looking to move to Passwordless auth there are a lot of great resources on the web. The FIDO alliance website is a great first stop. There are also numerous security vendors providing packaged solutions and most cloud providers have support for it – either as complete solutions or building blocks that can be wired together without too much difficulty. For anyone thinking about moving to Passwordless authentication for their apps I hope this article has been useful and good luck!